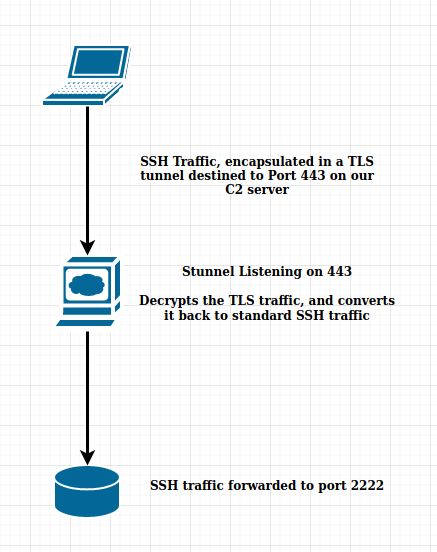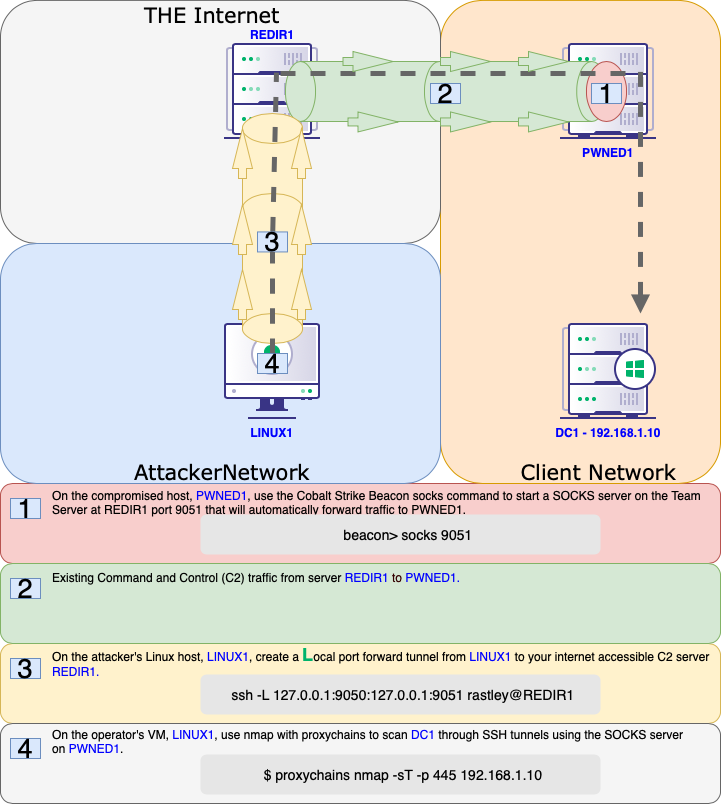
Offensive Security Guide to SSH Tunnels and Proxies | by Russel Van Tuyl | Posts By SpecterOps Team Members
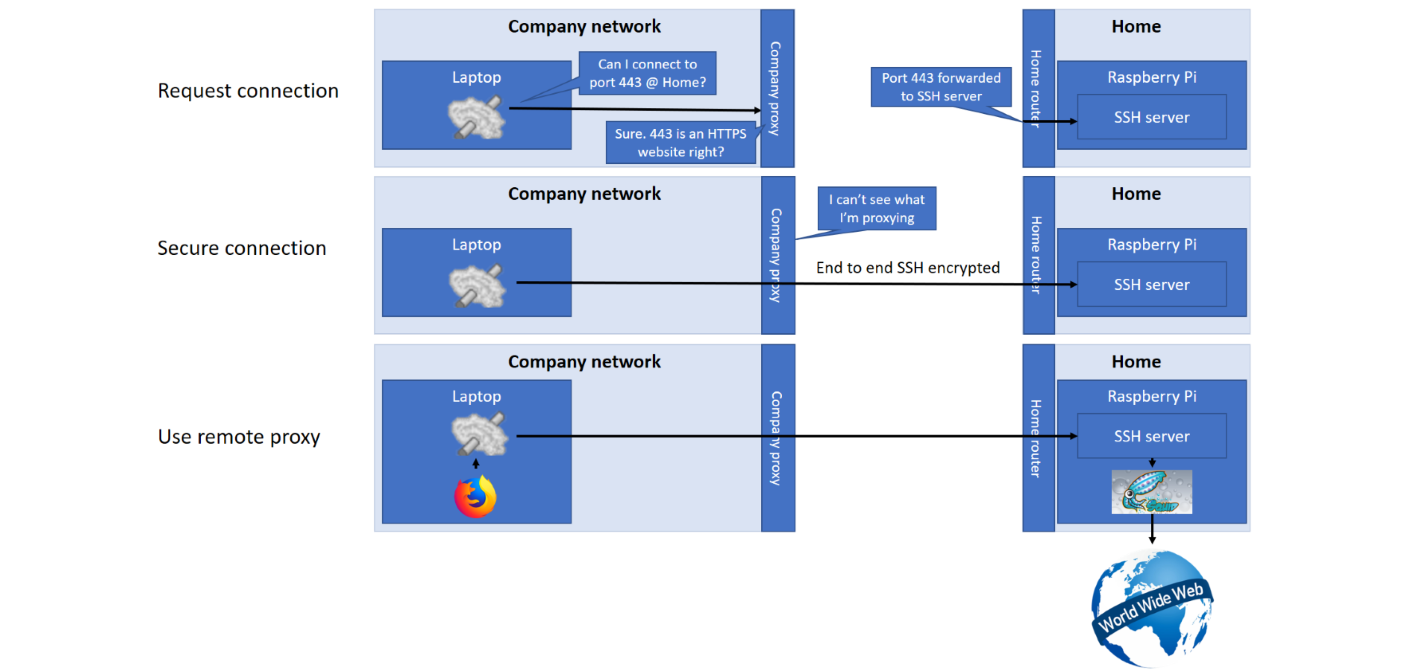
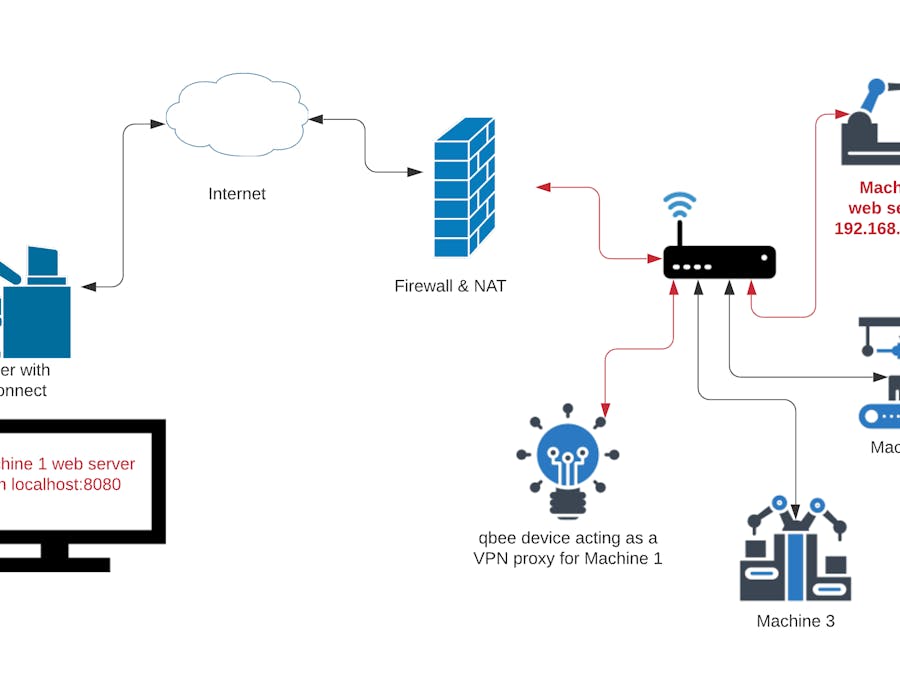
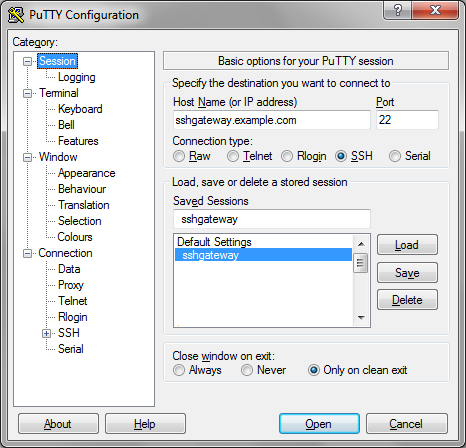
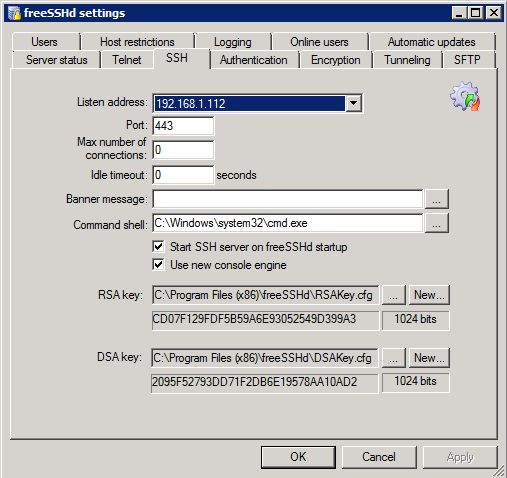
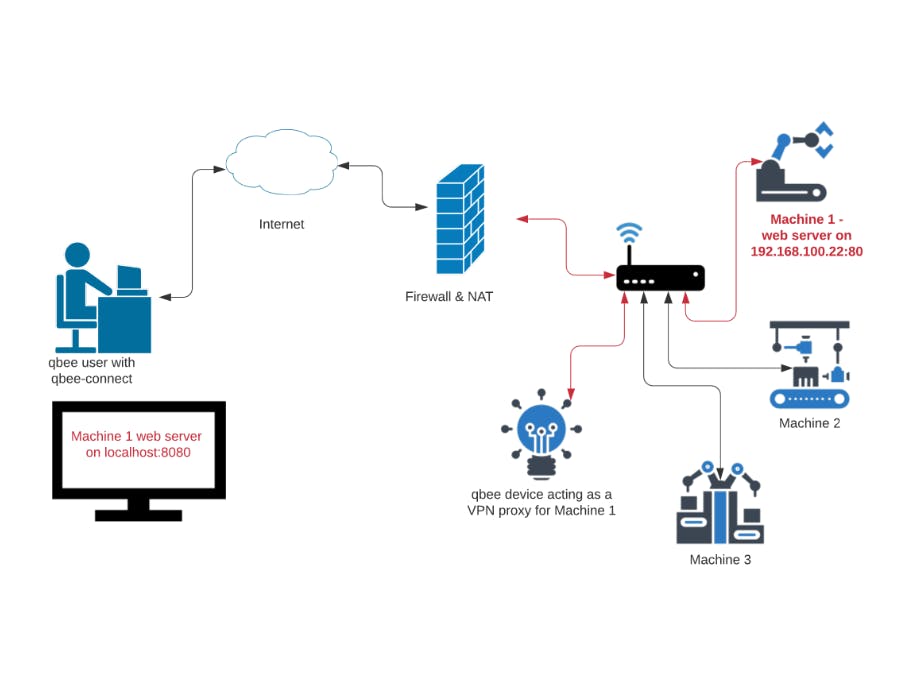
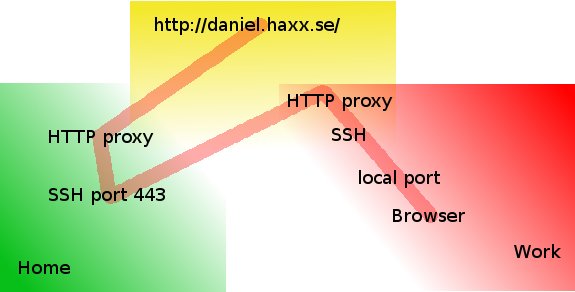
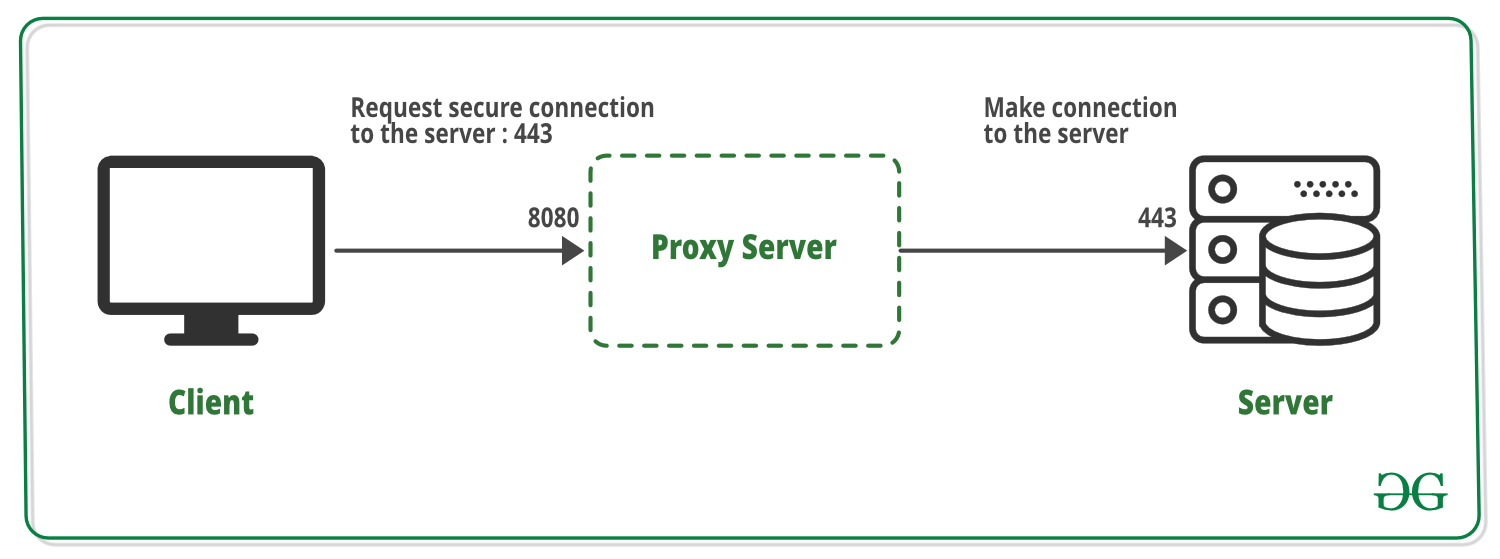
Security How to securely access remote content without using a VPN: Use a proxy server accessed through an SSH tunnel - AMIS, Data Driven Blog - Oracle & Microsoft Azure

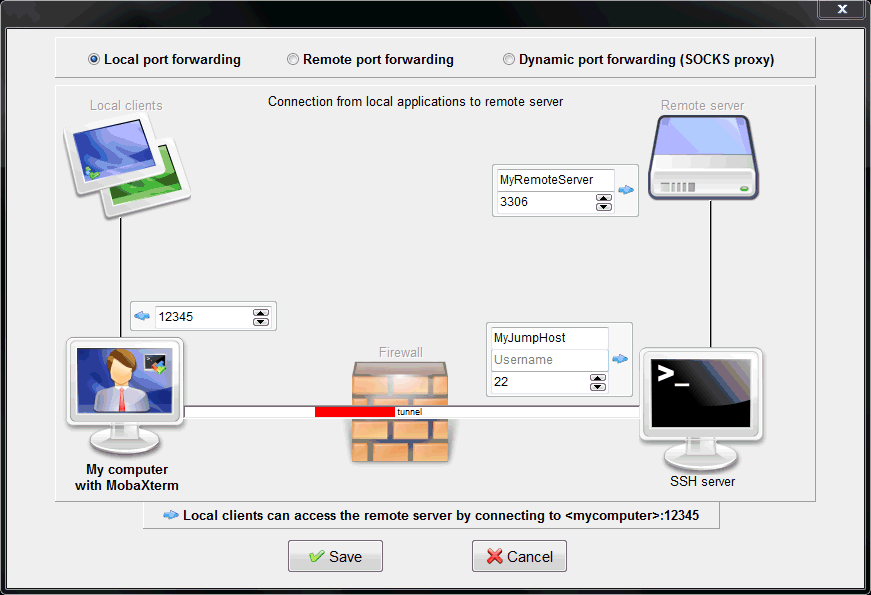
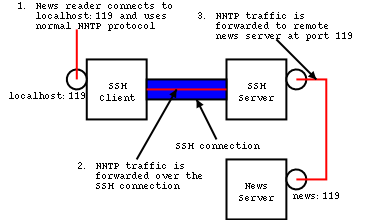
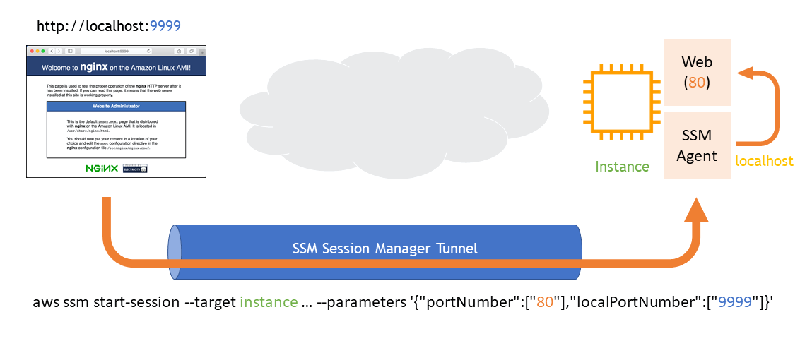
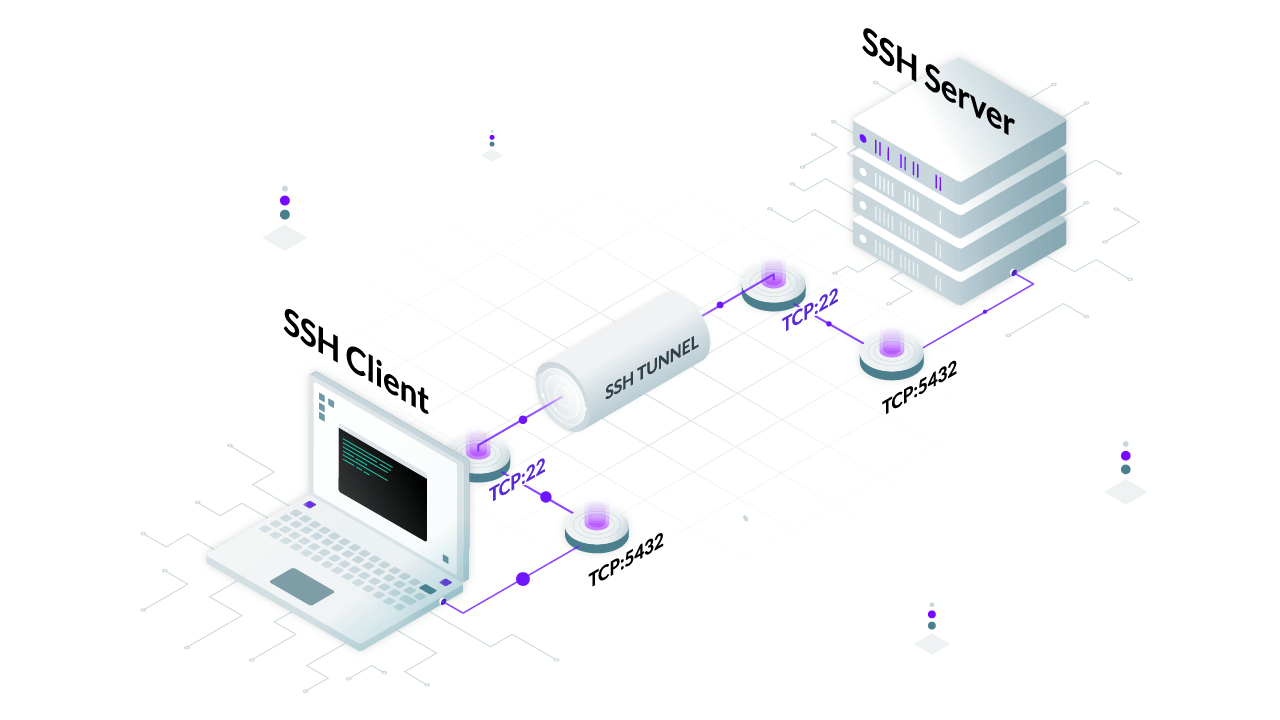
Tunneling application layer traffic through SSH – a method to bypass network restrictions – AppDelivery